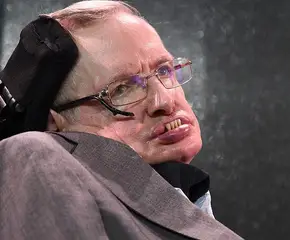
Edward Snowden speaks to a student group by video conference in 2015. Source: Gage Skidmore
On May 20, 2013, Edward Snowden boarded a flight from Hawaii to Hong Kong. The laptop and thumb drives he carried with him contained hundreds of thousands of secret government documents. In a Hong Kong hotel room, he met with journalists and a filmmaker named Laura Poitras, and together they began working through the documents Snowden had taken from the National Security Agency (NSA). At the time, Snowden was 29 years old.
Snowden entrusted his trove of files to journalists, who have steadily released details of how the United States collects and uses data via its spy agencies. Since then, the public has learned a great deal about the vast, secretive operations of the U.S. government and the NSA. According to Snowden’s files, the NSA has sought to “aggressively pursue legal authorities and a policy framework mapped more fully to the information age” with the aim of accessing data shared over the internet by “anyone, anytime, anywhere.”
Empowered by the President and Congress – and with tacit support from the American people – U.S. spy agencies, including the NSA, expanded their programs massively following the September 11th, 2001 terrorist attacks. The NSA’s collusion with telecom companies, particularly Verizon, AT&T, and Sprint, expanded again after the 2013 Boston Marathon bombing.

President Bush signs the Patriot Act into law on October 26, 2001. The Act greatly expanded the government’s authority to spy on its own citizens while reducing checks and balances on those powers. Barack Obama reauthorized it in 2011. Source: Wikipedia
These corporate partnerships and numerous additional NSA initiatives have focused on sweeping up as much “Sigint” (or “signals intelligence,” a bureaucratic name for electronic communications) as possible. The programs below are among the most expansive spying tools any government in history has ever used.
PRISM
Launched in 2007, PRISM acquires user data from the giants of the U.S. tech industry, including Google, Facebook, Microsoft, Skype, and Apple. Foreign Intelligence Surveillance Court secret orders required these companies to upload user data to NSA servers. According to internal NSA files published by the Washington Post, PRISM sweeps up emails, chats (including text, voice, and video); user videos; photos; stored online data; file sharing; login information, and social network data. It is, as the Post explains, “the number one source of raw intelligence used for NSA analytic reports.”

NSA Headquarters in Ft. Meade, Maryland Source: Getty Images
PRISM had 117,000 “active surveillance targets” in April 2013, but the program has collected information from tens of millions of Internet users, all of which can be accessed by low-level analysts without court approval. As Snowden told the Post, these analysts “quite literally can watch your ideas form as you type.”