Boundless Informant
This tool categorized and indexed the data collected by NSA through PRISM, Tempora, MUSCULAR, Dishfire, and other spy programs. The indexing included country information, and the NSA used this information to create a so-called “heat map” that showed in red where the largest intercepts were occurring.
“Patterns of Life” and the Drone Assassination Program
The NSA acquired the capabilities described above in the name of national security and with the legal (though perhaps not constitutional) authorization provided by the broad expansions of the U.S. security apparatus after 9/11. Defenders of the program often say that the collection of metadata has allowed the U.S. government to capture or kill dozens of dangerous terrorists.
But one of the most disturbing applications of NSA data collection – more concerning than the database of millions of faces from digital pictures or the tracking of visits to porn sites in an effort to “call into question a radicalizer’s devotion to the jihadist cause” – is the use of data to construct “patterns of life” that go on to form the basis of targeted killings.

‘Drone strikes have been sold to the American public on the claim that they’re ‘precise.’ But they are only as precise as the intelligence that feeds them.’ Source: Khaled Abdullah
In operations code-named GILGAMESH, SHENANIGANS, and VICTORYDANCE, the NSA, the Central Intelligence Agency (CIA), and the Joint Special Operations Command (JSOC) have used metadata collection and tracking to launch deadly assaults on targets in the Middle East and South Asia.
As Jeremy Scahill and Glenn Greenwald report at The Intercept, the NSA “is using complex analysis of electronic surveillance, rather than human intelligence, as the primary method to locate targets for lethal drone strikes – an unreliable tactic that results in the deaths of innocent or unidentified people.”
In other words, what is targeted in an attack is often not a particular individual but a SIM-card inside of a cell phone. Anyone can turn out to be holding the phone during an attack, even children, as has happened according to the authors’ reporting.
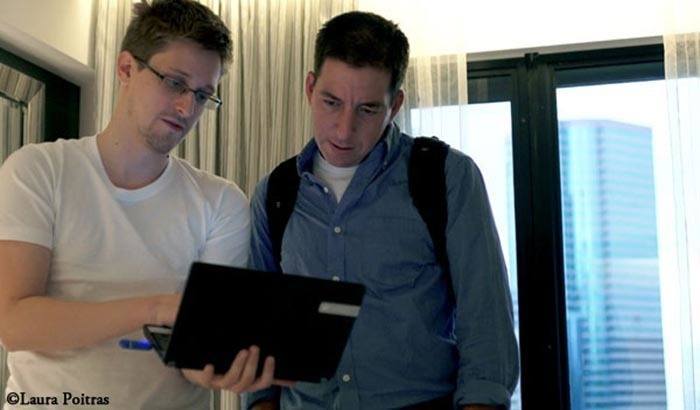
Edward Snowden and Glenn Greenwald, a Guardian journalist instrumental in bringing Snowden’s findings to the public Source: Lauren Poitras
Of course, none of these revelations and subsequent reports would have been possible without Snowden’s initial leak of documents in 2013. After spending several weeks in Hong Kong, Snowden flew to Moscow with the intentions of continuing on. But by then his passport had been cancelled, and he remained – and still remains – in Russia. He may not have expected to end up in Moscow, but Snowden realized he would likely not be able to return to the United States when he traveled to Hong Kong. As he told The Guardian, “I do not expect to see home again, though that is what I want.”